|
Size: 353
Comment:
|
← Revision 76 as of 2025-05-11 08:48:11 ⇥
Size: 8072
Comment:
|
| Deletions are marked like this. | Additions are marked like this. |
| Line 1: | Line 1: |
| = KeePassXC = {{attachment:keepassx.png}} <<TableOfContents>> * Background information: https://www.heise.de/news/Open-Source-Adventskalender-Der-Passwort-Manager-KeePass-6288780.html == Features == * Different passwords for different accounts. * MFA for modern accounts/services- this becomes so easy, use it wherever it is possible. * No single device dependency. Your passwords are where you are. * Splitted security levels (multiple vaults). * Awesome browser integration. * Sharing credentials (multiple vaults, shared via cloud storage). E.g. a) team: sharing credentials, b) family: shared WLAN password, children school accounts. |
|
| Line 3: | Line 20: |
| KeePassX is a tool to store and manage passwords. It is freely available for Linux/MacOS/Windows from http://www.keepassx.org/ | KeePassXC is a tool to store and manage passwords. Apps are freely available for |
| Line 5: | Line 22: |
| == How KeePassX works == | * MacOS/Windows/Linux - KeePassXC: https://keepassxc.org/. * Android: [[https://play.google.com/store/apps/details?id=com.kunzisoft.keepass.free|KeepassDX]] * iOS - https://keepassium.com/ |
| Line 7: | Line 26: |
| * KeePassX can create/open/edit/save password-databases. * A password-database is basically an encrypted file, where you can store your various usernames/passwords/URLs. |
Mobile Integration: * We have tested KeePassXC on mobile devices only very roughly. * The integration is not as good ('simple to use') as on the desktop app or in the browser. * Never the less: most persons see's it as an advantage to have the personal vault on their mobile device accessible. == How KeePassXC works == * KeePassXC create/open/edit/save password-vaults in a single file. * A password-vault is basically an encrypted file, where you can store your various usernames/passwords/URLs and also attachments like pictures or other important / private documents. * A password-vault can only be opened if you know the Master-Password. The Master Password is the key to all your stored passwords. * If you forgot your Master-Password, you cannot access your stored passwords anymore. * Encryption -- either the Advanced Encryption Standard (AES) or the Twofish algorithm are used for encryption of the vault in 256 bit sized increments * All features: http://www.keepassx.org/features/ == Creating a Password Vault == * Click on "File" --> "New Database..." * You will be prompted to set a master key. Input your master password (the master password for all your other stored passwords). Then click "OK" * Repeat your master password. click "OK". * Chose a group. (Standard choices are Internet of eMail. You can also create your own groups). * Click on "Entries" --> "Add New Entry..." * Input the information you need * Title: a short description of the entry * Username: your username * URL: on what homepage do you need the password * Password: your password * Repeat: repeat your password * Comment: a longer description of the entry * Click on "File" --> "Save Database" * Chose a location and a name for your password database. click "OK" == Best practice: Sync Vault via cloud == * Only use a cloud service if you need to sync your passwords across several devices! (Recommendation: yes, use a cloud service) * Decide on your own: * Pro 'cloud': * all of your confidental data on all devices. * implicit backups (data on multiple devices, and also in the cloud). * Contra 'cloud': * all of your confidental data on all devices - higher chance that your (encrypted) vaults are accessible to others. * If your cloud access is compromised or the cloud service provider is compromised: the thief owns the (enrypted) vault. * US based cloud provider like Google Drive, Dropbox, Apple iDrive, Microsoft !OneDrive: * Those services are very attractive to hackers. * The NSA has the right to get all data from US companies. After Snowden it's for sure, the NSA is not friendly. * Rule of thumb: '''Don't use US hosted / company based services''' for confidential data. * Local cloud storage provider: * [[https://drive.switch.ch]] - Switch Eduction cloud service - '''switchdrive''' * [[https://drive.math.uzh.ch]] - I-MATH * How to: * On all devices where you like to sync your KeePassXC Vault file, install and configure [[drive.math.uzh.ch]] * Open the KeePassXC vault file on all of your devices directly from the cloud folder. * Automatic merge of vault: Even if KeePassXC has a vault opened, changes on a different device (e.g. phone) and sync via cloud, becomes immediately active. * If you work in a team: no change, everyone can open the local copy - changes will be merged. = Browser integration / MFA Setup / Passkeys = * KeePassXC can be used from within a browser (Chrome, Chromium, Firefox, Vivaldi, Brave, ...) * Browser connection to KeePassXC is nice: different browsers offer the same accounts/credentials - if synced via cloud than also on different computers. * TOTP service (one time token). * Passkeys support. * Again, think on this: There is only one source of truth (=one KeePassXC vault), in all browsers you have all your credentials available. Finally: * '''no more MS-Authenticator app needed''' * '''no more single device dependency''' (Phone at home, ...) * '''login to any MFA protected website without a mobile phone''' - Biggest advantage: your second token are controlled by you, not any provider. * '''still secure''' - the second factor is now your KeePassXC. == Settings == {{attachment:kp-browserintegration.png}} * Settings > Browser Integration > Enable integration ...: Chrome, Firefox, ... == Browser Plugin == * Install the corresponding browser plugin (links to app store: check settings dialog '5' ) * Passkeys have to explicitly enabled in the browser plugin: {{attachment:kp-passskeys.png}} == Regular Username / Password == * Take care that the KeePassXC icon on the top right is 'green' = connection to vault is active. * Open the login page in the browser. {{attachment:kp-fill.png}} * Click on the small green kp icon. * Choose the account. == MFA == === TOTP === * To use TOTP with Microsoft Office 365 login: Add another (than MS-Authenticator-) app, as second factor [[MFA/Microsoft_Authentication#Add_third_party_TOTP_app|How To]] {{attachment:kp-totp.png}} * Add [[https://en.wikipedia.org/wiki/Time-based_one-time_password|TOTP]] functionality to individual accounts: Account > right mouse click > TOTP > Setup TOTP * On a MFA-TOTP secured login website, just login as usual with KeePassXC, on the next page, where the one time token is requested, click again on the green symbol. Hint: * On the `TOTP setup` you have to provide the 'shared secret'. * The shared scecret is provided by the website which hosts the login, typically where the MFA can be configured. * Either in plaintext like 'ABCD EFGH 1234 IJKL 5678 MNOP QRST UV89'. * As a QR code to scan. * Here sometimes it's a URL or a `fido` string. * If it is not in plaintext in the URL, hopefully the assigned app (=keepassdx) opens. * Option: be creative - scan the QR, look at the url (or send the URL via 'share' to yourself): you should see the shared secret as an argument in the URL. === Passkey === * [[https://en.wikipedia.org/wiki/WebAuthn|Passkey / webauthn]] are offered as an additional way to use MFA. * Passkeys offers more security than TOTP and should be used when possible. * But: Some websites work better than others. E.g. eduid.ch is ok, gitlab is ok but with popup, Microsoft is broken for Linux/Chrome/KeePassXC, ... === Recovery Keys === * Some services offers recovery keys. * Copy the keys in corresponding account record in KeePassXC. * If you used a key (it's burnt now), remove it from the list (if there was only one key, update it with the new one). == Same account / different URLs == * Some services, especially Microsoft (https://login.live.com/, https://login.microsoftonline.com/), uses different URLs to login. * Per account, add further URLs: {{attachment:kp-addurl.png}} * This is very '''powerful''' - add as many URLs you like to the same account record - the helps to keep your vault clean! |
KeePassXC
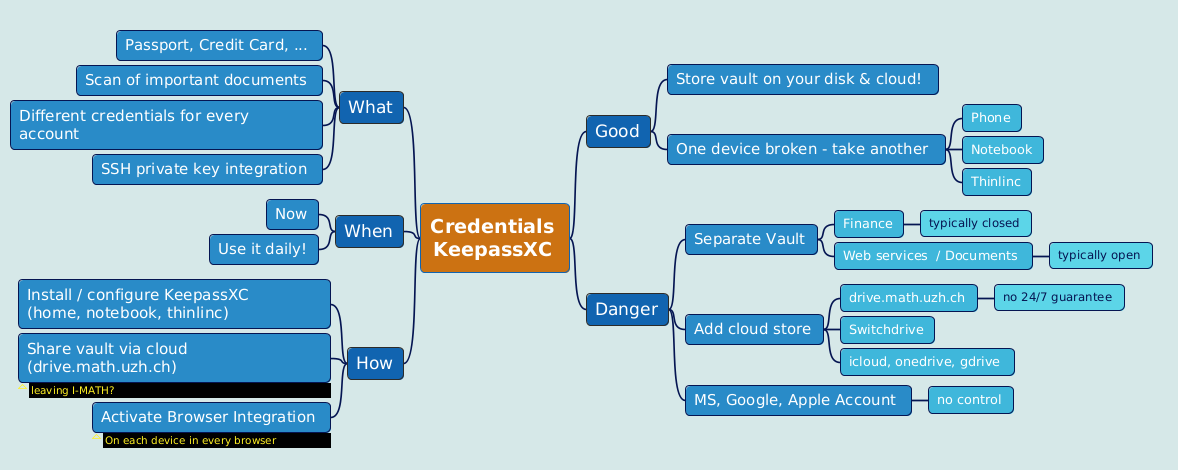
Contents
Background information: https://www.heise.de/news/Open-Source-Adventskalender-Der-Passwort-Manager-KeePass-6288780.html
Features
- Different passwords for different accounts.
- MFA for modern accounts/services- this becomes so easy, use it wherever it is possible.
- No single device dependency. Your passwords are where you are.
- Splitted security levels (multiple vaults).
- Awesome browser integration.
- Sharing credentials (multiple vaults, shared via cloud storage). E.g. a) team: sharing credentials, b) family: shared WLAN password, children school accounts.
Description
KeePassXC is a tool to store and manage passwords. Apps are freely available for
MacOS/Windows/Linux - KeePassXC: https://keepassxc.org/.
Android: KeepassDX
iOS - https://keepassium.com/
Mobile Integration:
- We have tested KeePassXC on mobile devices only very roughly.
- The integration is not as good ('simple to use') as on the desktop app or in the browser.
- Never the less: most persons see's it as an advantage to have the personal vault on their mobile device accessible.
How KeePassXC works
- KeePassXC create/open/edit/save password-vaults in a single file.
- A password-vault is basically an encrypted file, where you can store your various usernames/passwords/URLs and also attachments like pictures or other important / private documents.
- A password-vault can only be opened if you know the Master-Password. The Master Password is the key to all your stored passwords.
- If you forgot your Master-Password, you cannot access your stored passwords anymore.
- Encryption -- either the Advanced Encryption Standard (AES) or the Twofish algorithm are used for encryption of the vault in 256 bit sized increments
All features: http://www.keepassx.org/features/
Creating a Password Vault
Click on "File" --> "New Database..."
- You will be prompted to set a master key. Input your master password (the master password for all your other stored passwords). Then click "OK"
- Repeat your master password. click "OK".
- Chose a group. (Standard choices are Internet of eMail. You can also create your own groups).
Click on "Entries" --> "Add New Entry..."
- Input the information you need
- Title: a short description of the entry
- Username: your username
- URL: on what homepage do you need the password
- Password: your password
- Repeat: repeat your password
- Comment: a longer description of the entry
Click on "File" --> "Save Database"
- Chose a location and a name for your password database. click "OK"
Best practice: Sync Vault via cloud
- Only use a cloud service if you need to sync your passwords across several devices! (Recommendation: yes, use a cloud service)
- Decide on your own:
- Pro 'cloud':
- all of your confidental data on all devices.
- implicit backups (data on multiple devices, and also in the cloud).
- Contra 'cloud':
- all of your confidental data on all devices - higher chance that your (encrypted) vaults are accessible to others.
- If your cloud access is compromised or the cloud service provider is compromised: the thief owns the (enrypted) vault.
- Pro 'cloud':
US based cloud provider like Google Drive, Dropbox, Apple iDrive, Microsoft OneDrive:
- Those services are very attractive to hackers.
- The NSA has the right to get all data from US companies. After Snowden it's for sure, the NSA is not friendly.
Rule of thumb: Don't use US hosted / company based services for confidential data.
- Local cloud storage provider:
https://drive.switch.ch - Switch Eduction cloud service - switchdrive
https://drive.math.uzh.ch - I-MATH
- How to:
On all devices where you like to sync your KeePassXC Vault file, install and configure drive.math.uzh.ch
- Open the KeePassXC vault file on all of your devices directly from the cloud folder.
- Automatic merge of vault: Even if KeePassXC has a vault opened, changes on a different device (e.g. phone) and sync via cloud, becomes immediately active.
- If you work in a team: no change, everyone can open the local copy - changes will be merged.
Browser integration / MFA Setup / Passkeys
- KeePassXC can be used from within a browser (Chrome, Chromium, Firefox, Vivaldi, Brave, ...)
- Browser connection to KeePassXC is nice: different browsers offer the same accounts/credentials - if synced via cloud than also on different computers.
- TOTP service (one time token).
- Passkeys support.
- Again, think on this: There is only one source of truth (=one KeePassXC vault), in all browsers you have all your credentials available.
Finally:
no more MS-Authenticator app needed
no more single device dependency (Phone at home, ...)
login to any MFA protected website without a mobile phone - Biggest advantage: your second token are controlled by you, not any provider.
still secure - the second factor is now your KeePassXC.
Settings
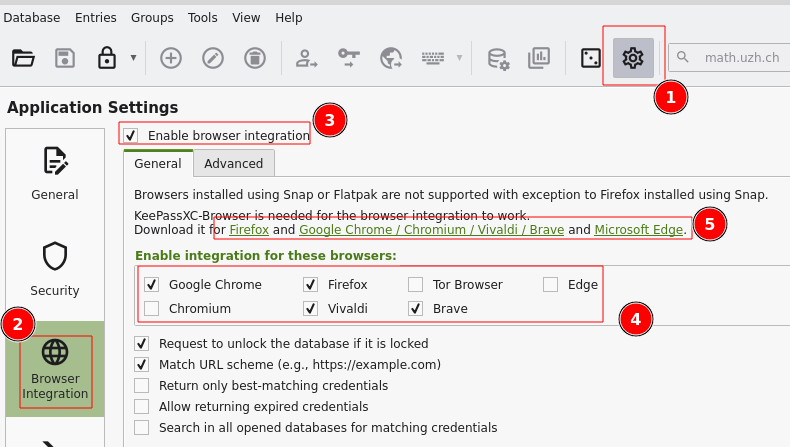
Settings > Browser Integration > Enable integration ...: Chrome, Firefox, ...
Browser Plugin
- Install the corresponding browser plugin (links to app store: check settings dialog '5' )
- Passkeys have to explicitly enabled in the browser plugin:

Regular Username / Password
- Take care that the KeePassXC icon on the top right is 'green' = connection to vault is active.
- Open the login page in the browser.
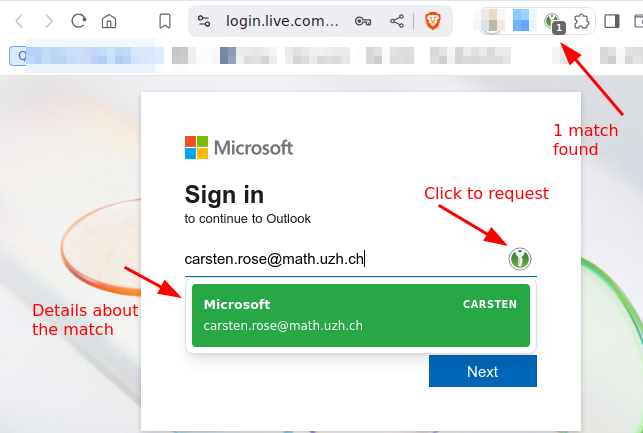
- Click on the small green kp icon.
- Choose the account.
MFA
TOTP
To use TOTP with Microsoft Office 365 login: Add another (than MS-Authenticator-) app, as second factor How To
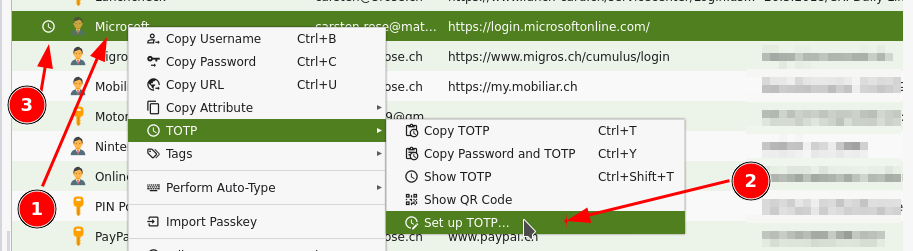
Add TOTP functionality to individual accounts: Account > right mouse click > TOTP > Setup TOTP
- On a MFA-TOTP secured login website, just login as usual with KeePassXC, on the next page, where the one time token is requested, click again on the green symbol.
Hint:
On the TOTP setup you have to provide the 'shared secret'.
- The shared scecret is provided by the website which hosts the login, typically where the MFA can be configured.
- Either in plaintext like 'ABCD EFGH 1234 IJKL 5678 MNOP QRST UV89'.
- As a QR code to scan.
Here sometimes it's a URL or a fido string.
- If it is not in plaintext in the URL, hopefully the assigned app (=keepassdx) opens.
- Option: be creative - scan the QR, look at the url (or send the URL via 'share' to yourself): you should see the shared secret as an argument in the URL.
Passkey
Passkey / webauthn are offered as an additional way to use MFA.
- Passkeys offers more security than TOTP and should be used when possible.
- But: Some websites work better than others. E.g. eduid.ch is ok, gitlab is ok but with popup, Microsoft is broken for Linux/Chrome/KeePassXC, ...
Recovery Keys
- Some services offers recovery keys.
- Copy the keys in corresponding account record in KeePassXC.
- If you used a key (it's burnt now), remove it from the list (if there was only one key, update it with the new one).
Same account / different URLs
Some services, especially Microsoft (https://login.live.com/, https://login.microsoftonline.com/), uses different URLs to login.
- Per account, add further URLs:
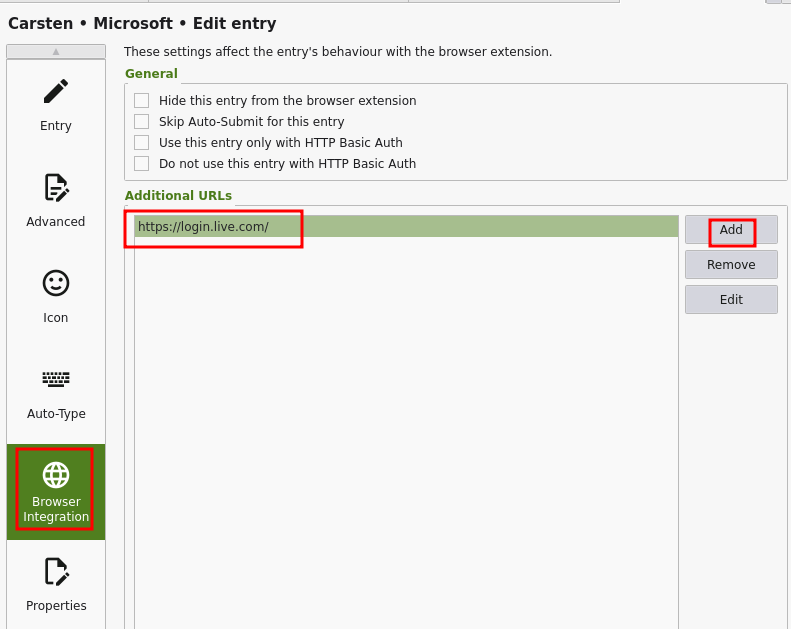
This is very powerful - add as many URLs you like to the same account record - the helps to keep your vault clean!
